Subtotal $0.00
A cyber security assessment is a strategic review of your organisation's security posture, designed to uncover weaknesses before an attacker can exploit them. It connects technical vulnerabilities—like unpatched software or misconfigured cloud services—to tangible business risks, such as operational downtime, data breaches, or reputational damage. The goal is to move beyond abstract threats and create a clear, actionable plan to strengthen your defences.
Why a Security Assessment is a Business Essential

Many organisations still treat security assessments as a technical chore or a compliance checkbox. In reality, a cyber security assessment is a cornerstone of modern business resilience. It provides an objective, evidence-based snapshot of your defences, finally answering the critical question: "How secure are we, really?"
To effectively understand the landscape of threats and vulnerabilities your business faces, a thorough cybersecurity risk assessment serves as the bedrock of any credible security strategy. This isn't about guesswork; it's about gaining data-driven clarity.
That clarity is more critical than ever. The latest UK government survey revealed a startling statistic: 43% of businesses experienced a cyber security breach in the last year. More concerning is that only 29% of businesses conduct formal cyber risk assessments. This highlights a significant gap between the rising threat level and organisational preparedness.
A well-executed assessment delivers tangible business outcomes, not just a technical report. It enables you to:
- Identify Hidden Risks: Uncover vulnerabilities in your network, applications, and cloud environments that automated tools often miss.
- Prioritise Security Investments: Guide your budget toward fixing the most critical issues first, ensuring maximum return on investment.
- Strengthen Compliance: Provide the necessary evidence to meet regulatory requirements and achieve certifications like Cyber Essentials.
Ultimately, a professional assessment is less about finding faults and more about building a strategic roadmap toward a stronger, more resilient organisation.
Not all cyber security assessments are the same. Choosing the right type depends on your specific goals, budget, and the operational risks your business faces. Selecting the wrong approach is like calling an electrician to fix a leak—you might get an opinion, but it won't solve the underlying problem.
Think of it as selecting the right tool for the job. A Vulnerability Scan is your automated, routine health check. It is quick, cost-effective, and effective at identifying known security flaws like outdated software or common misconfigurations before they can be exploited. It essentially asks, "Are there any obvious, unlocked doors?"
Going Deeper Than Automated Scans
But what if you need to understand how your defences would perform against a motivated attacker? That is where a Penetration Test becomes invaluable. This is a simulated, ethical cyber-attack where experts actively attempt to breach your systems. It moves beyond identifying theoretical weaknesses to actively exploiting them, demonstrating the real-world impact a breach could have on your business.
A penetration test answers a different, and arguably more critical, business question: "If someone actively tries to break in, how far could they get, and what damage could they do?" That insight is crucial for prioritising security spending effectively.
Specialised Assessments for Today's Challenges
As business operations evolve, security measures must adapt. A one-size-fits-all assessment is no longer sufficient.
- Azure Security Reviews: If your business relies on Microsoft's cloud platform, a generic scan will miss platform-specific nuances. This review is tailored for Azure, analysing everything from identity and access management to network configurations and data protection against established best practices.
- Cyber Essentials Audits: For any UK business, achieving Cyber Essentials or Cyber Essentials Plus is a powerful signal to customers and partners that you take security seriously. This audit validates that your defences are robust against the most common cyber threats and is often a prerequisite for government contracts.
- Zero Trust Readiness Assessments: If you are transitioning from a traditional perimeter-based security model, this assessment is essential. It evaluates how prepared your architecture is to adopt a modern "never trust, always verify" security framework.
Understanding these distinctions is the first step toward building a smarter security strategy. To help navigate the options, you can explore the different types of cyber security assessments in more detail. Each provides unique insights, helping you build a defence that is truly fit for purpose.
A Look Inside the Assessment Process
A professional cyber security assessment should be a transparent, collaborative process that translates technical complexity into actionable business intelligence. An experienced partner demystifies the process, providing a clear path from risk identification to remediation.
The process begins with Scoping. This is a collaborative phase where we define precisely which systems will be tested and, more importantly, why they matter to the business. Aligning on objectives from the start ensures the final report is relevant and delivers genuine value. From there, we proceed to Information Gathering, where we map your digital footprint to understand what an attacker would see.
Next is the Execution phase—the hands-on testing where we actively probe for vulnerabilities. However, the process concludes with the Reporting stage. This is far more than a simple list of technical flaws; it is a strategic document that translates findings into plain language, complete with prioritised, practical recommendations.
This diagram provides a high-level overview of a typical assessment workflow, from initial scanning to compliance verification.
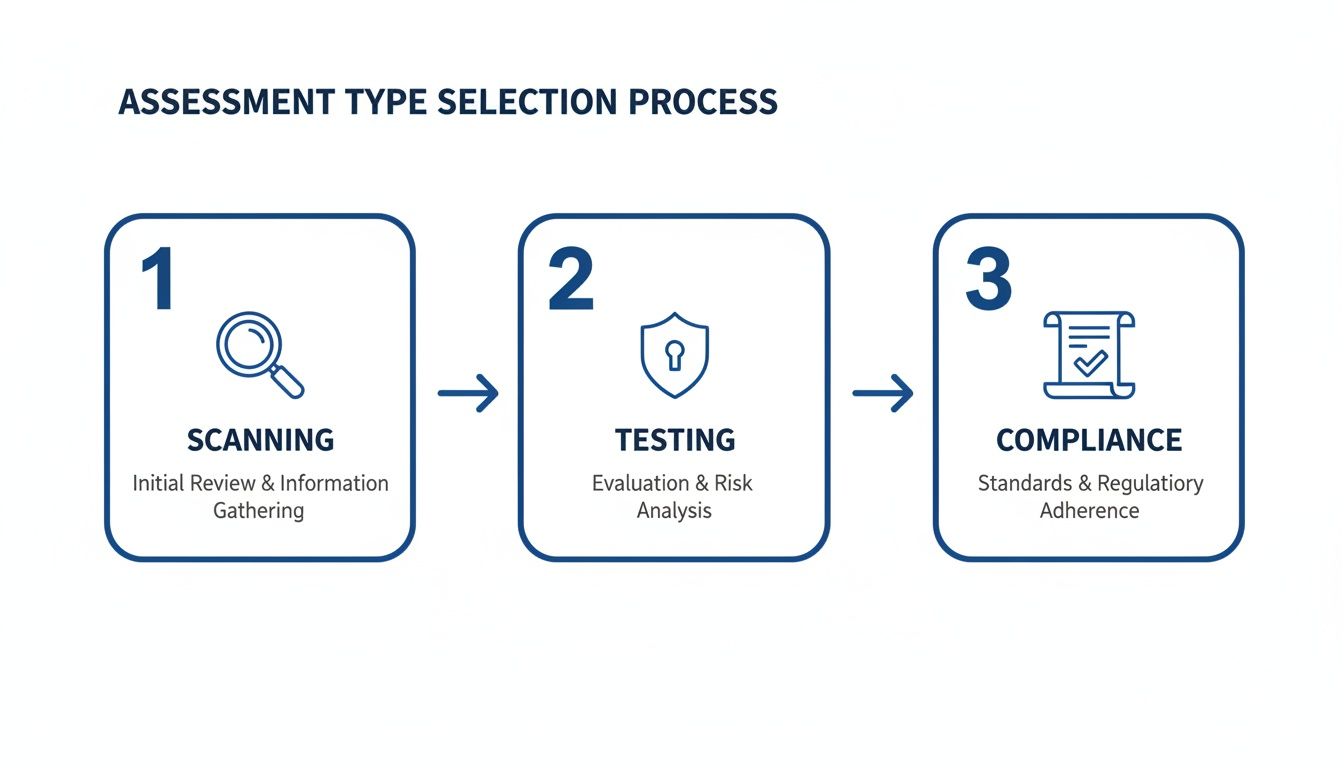
As illustrated, a comprehensive assessment extends beyond finding vulnerabilities; it validates your security posture against recognised industry standards.
While this structured approach is becoming more widespread, troubling gaps persist. Although the number of UK SMBs conducting their own cyber risk assessments has risen to 48%, the number assessing their suppliers has fallen to just 21%. This decline leaves supply chains dangerously exposed. You can read the full analysis in the UK cyber security breaches in 2025 report.
This gap underscores why a comprehensive process is so critical, often supported by ongoing cyber security managed services to maintain and enhance resilience over time.
Making Sense of Your Assessment Report
The true value of any cyber security assessment lies not in the testing but in the final report. A technical list of vulnerabilities is useless without context. A high-quality report translates complex findings into clear, business-oriented language, providing the clarity needed for informed decision-making.
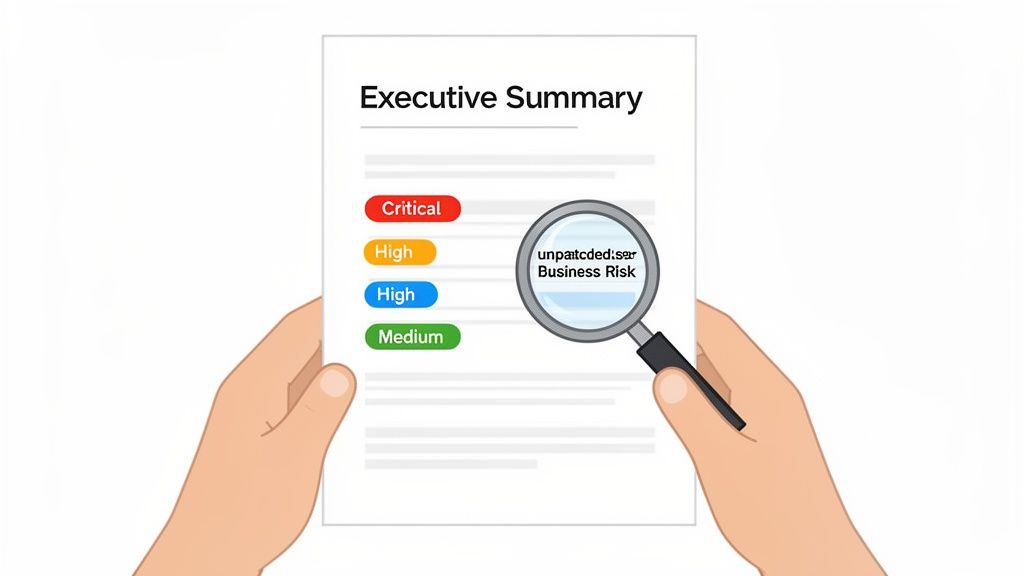
A strong deliverable should be structured to serve different stakeholders within your organisation. It should begin with an Executive Summary—a concise, jargon-free overview for leadership that outlines key risks and their potential impact on the business. This is followed by detailed Technical Findings, which provide your IT team with the specific information they need to address the issues.
Turning Data Into Decisions
The most critical component is the Remediation Plan. This should not be a simple list of problems but a prioritised roadmap for solutions. Vulnerabilities are typically categorised by severity—such as Critical, High, and Medium—based on their real-world impact on your operations.
For example, a finding like an ‘unpatched server’ is more than a technical detail. The report must frame it as a direct business risk: ‘potential for a ransomware attack that could halt all operations’. This is the kind of context that drives meaningful action.
A strong assessment report transforms abstract data into a clear action plan. It connects a technical vulnerability to a direct business outcome, making it impossible to ignore and easy to prioritise.
This demand for clear, actionable intelligence is fuelling significant growth in the sector. The UK's cyber security market generated £13.2 billion in 2025, a 12% increase driven by the relentless need to defend against evolving threats. You can explore the full 2025 Cyber Security Sectoral Analysis Report for further details on this trend. A quality report is the vital first step in converting assessment data into a stronger defence.
Turning Your Assessment Insights Into Action
Receiving your cyber security assessment report is the starting point, not the finish line. True value is realised when you translate its findings into a more resilient security posture. This begins with a clear remediation plan that converts technical details into prioritised, actionable tasks for your team.
The goal is not just to patch the immediate vulnerabilities identified in the assessment. It is to evolve from a one-time project into a continuous cycle of improvement, embedding sound security practices into your daily IT operations. This is how you build lasting cyber resilience—by using the assessment as a foundation for a proactive, long-term security journey.
The most effective approach treats the assessment as a baseline for future progress. It’s not just about patching holes; it’s about fundamentally improving your security culture and processes over the long term.
To ensure your efforts are effective, it is crucial to establish baseline metrics for continuous improvement. This allows you to track meaningful progress over time. For many organisations, particularly those pursuing standards like Cyber Essentials, this structured approach is non-negotiable. You can learn more about this in our guide on what Cyber Essentials certification is.
Ultimately, expert guidance through this process helps ensure your defences evolve in step with the threat landscape, protecting your business for the long term.
Frequently Asked Questions
Here are practical answers to some of the most common questions businesses ask about cyber security assessments.
How Often Should We Run a Security Assessment?
The ideal frequency depends on your industry, risk profile, and the rate of change in your IT environment. For most businesses, a comprehensive assessment performed annually is a solid baseline.
However, this should be complemented by more frequent, automated vulnerability scans—quarterly or even monthly. This practice helps maintain a consistent security posture and identify new issues as they arise, without waiting for the annual review.
How Much Does a Cyber Security Assessment Cost?
The cost of a cyber security assessment varies significantly based on the scope and depth of the engagement. An automated vulnerability scan will naturally be less expensive than a manual, in-depth penetration test that requires weeks of an expert's time.
The best way to view it is as an investment in risk mitigation. The cost is tailored to the complexity of the systems being protected. A small local business has different requirements—and a different budget—than a multinational corporation handling sensitive financial data.
What's the Difference Between a Vulnerability Scan and a Pen Test?
This is an excellent and common question. A simple analogy helps clarify the distinction.
A vulnerability scan is like checking every door and window in your office building to see if any are unlocked. It is an automated process that quickly identifies known weaknesses and potential entry points. It is fast, efficient, and provides a broad overview of your security posture.
A penetration test, on the other hand, is like hiring a security expert to actively try to break in. They won't just check for unlocked doors; they will attempt to pick the locks, find weak spots in the walls, and determine how far they can get once inside.
Both are incredibly valuable but serve different purposes. A scan provides breadth, while a penetration test delivers depth.